By Kiki Schirr, {grow} Contributing Columnist
Marketing and the dark web is a hot topic.
In the last two years, I’ve seen marketers start to eye the dark web with a new hunger. Maybe as we deal with Content Shock, restless marketers are searching for a new frontier. Or maybe they’ve conquered listening to brand chatter on even the most notorious niche Internet social venues, like Reddit, Mastodon, or Nextdoor. Perhaps they’re seeking a new challenge.
Whatever their motivation, the decision to pursue the dark web should not be taken lightly, as it requires a rare set of technical skills and is not without risk.
Is the dark web only for criminals?
You might have heard of the dark web in the context of the joint IRS, DEA, and FBI takedown of the Silk Road, a dark web market mostly used to trade illegal drugs for cryptocurrency.
Since this bust, the dark web has had a sinister reputation. The Silk Road certainly deserves its notoriety. However, the constant press mentions of the most widely used dark web tool, The Onion Router (Tor), and the Silk Road in the same sentence has made having Tor on a computer look suspicious to regular Internet denizens.
But Tor was actually developed and funded in conjunction with the US government under Navy and DARPA research programs. It’s only a means of access, not an illegal site or marketplace.
And while the dark web is undoubtedly used primarily for illegal activities we also need to remember that what is illegal differs by country. By allowing people to organize a political discussion in an anonymous manner online, Tor might be facilitating something illegal in a totalitarian regime like North Korea, for example. And when that occurs, DARPA probably pats itself on the back.
But dealing Fentanyl is pretty abhorrent worldwide.
Still, there are plenty of people, many of whom privacy advocates or libertarians, who visit the dark web just to avoid being tracked online while they converse with friends. These sheltered conversations are making some brands salivate with curiosity.
Should your brand monitor the dark web?
The vast majority of companies should not have any presence on the dark web at this time. The risks currently outweigh the benefits for most types of business.
For now, the only type of brands that might find the risks of the dark web worthwhile would be those who seek recreational drug users, cryptocurrency libertarians, or anarchists as clients.
Even then, companies that approach the dark web should have a skilled staff of cybersecurity experts, a mandatory training course for anyone participating, and a written crisis policy prepared in advance.
However, constantly assessing new and developing platforms is integral to marketing strategy. So periodically you’ll want to reassess this decision, monitoring the potential of the dark web versus the risks to your company and staff.
This guide will help you master the basic information you’ll need to keep an eye on the dark web from afar, and to discuss it with others knowledgeably.
I’d like to start by taking some time to define dark vs deep web because I see many people use the terms interchangeably online. That is incorrect: the dark web is a small part of the deep web but they serve very different purposes and don’t technically even run on the same network.
A technical definition of the dark web
The dark web refers to a group of all unindexed overlay networks, known as dark nets or darknets, which are distributed systems inaccessible without a certain software and/or set of permissions.
That’s a lot of jargon in one paragraph, so let me break it down a bit by explaining the deep web and then contrasting the two. If you did understand that first definition or are only interested in the dark web, feel free to skip ahead to the section on why people use the dark web.
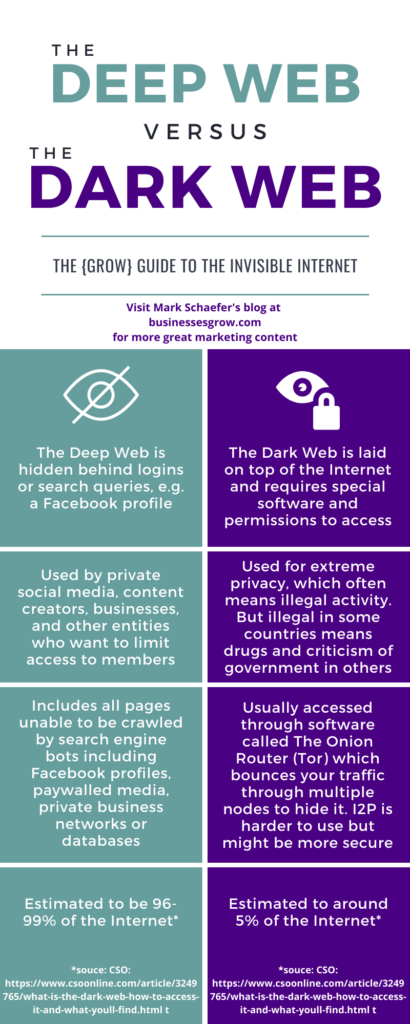
What is the deep web?
When you access the Internet through a standard browser like Safari or Firefox, most sites are built to be easy to navigate. Sites provide URL addresses to most of their content so that you can quickly arrive without doing a search, in the same way that you can give an address to a stranger or Uber and end up at the same destination without having to guide people to turn left at McDonald’s.
To extend the travel metaphor, search engines function like guidebooks. They work best when they can access all sites and from that pool steer people to the most useful pages. In order to provide this service, they list all content on the Internet by running bots that endlessly roam through the Internet, scraping data and recording URLs. At this point, some researchers claim that the majority of the traffic is bots crawling through pages or maliciously clicking on competitor’s ads.
If a site has a URL and doesn’t include a short bit of code in its header to limit search engine indexing, bots can add it to their data easily. However, a surprising amount of the Internet is behind a password, has that snippet of code that asks bots to kindly depart, or is limited by a search query within Flash or JavaScript, all of which deflect bot access.
Estimates on how much of the Internet is inaccessible to Google or other search engines like Duckduckgo vary, but are steadily increasing. I’d say a conservative estimate at this point is 90% of Internet content cannot be accessed by a search engine, but estimates reach 99% lately.
Why is the deep web not indexed?
90-99% of the Internet is an astounding number, especially when you consider how much data Google still has. At first this number might seem impossible but remember: except for Facebook business pages, all of Facebook is blocked from anyone who hasn’t logged in as a human being. LinkedIn is similarly shielded. Nextdoor, dating sites, company portals, shopping logins–many sites we use every day fall into this category.
Bots aren’t supposed to try to circumvent logins so anything you can’t see without entering your name and password is rendered invisible to Google.
(Safety tip side note: Security companies, criminals, and other data gathering institutions often try to get around these barriers. They can create fake profiles to access what they need. That’s why you get friend requests from accounts that are mimicking people you cared about but drifted away from — “I got locked out of my old account” they say. Be sure to ask them your high school nickname prior to adding them.)
So to summarize a brief definition, every site that can’t be reached with a bot, even ones as mundane as Facebook profile pages, fall under the umbrella of the “Deep Web.” How, then, does the dark web differ?
What is the dark web?
The dark web, unlike the deep web, is not an inaccessible corner of the Internet, it’s not really a part of the Internet at all. Instead, it’s what’s called an overlay network.
An example of an overlay network you’ve likely used would be at a library that restricts book catalogs from accessing the Internet themselves so that patrons don’t linger on their high-traffic catalogs. The catalog computers, the printers, and let’s say a regular computer are networked to communicate with each other and that network might occasionally access the Internet for updates, but the connections formed between them are not Internet connections.
Imagine for a moment that someone wanted to send a text message to one of the book catalogs. Unless that person could text the one Internet-enabled computer something that would then be passed to the catalog computer, it would be impossible.
The same is true for accessing dark web sites. Sites that are hosted on the Tor network (they end in .onion!) can’t be reached by typing in a URL on Firefox. Firefox can’t access their network. In order to connect to a .onion site, you have to use the Tor browser to get started.
The main benefit of the dark web and Tor or I2P is the anonymity they provide. Because I’m focusing on the dark web from a marketer’s perspective, I’m going to skip an explanation of how the provide anonymity, but if you’re interested, you can read more about anonymity here.
Why do people use the dark web?
There’s nothing scary about the regular Internet to the average user. Most people feel pretty safe behind a login page, enough to post pictures of their kid or flirt with a stranger. But to users of the dark web, who value privacy, a login page is actually worse in many ways. The more often you have to surrender data in order to access a site the more clear a self portrait you paint over time.
And while the memories of mere humans or iCloud are very limited (5 GB is not enough, Apple) Internet adservers never forget a face.
Want to see what I mean? There’s a simple test to see if you’ve already created a unique presence online that could only be you.
How to know if you need to step up your privacy efforts
A true privacy advocate would tell you everyone should step up their privacy efforts, but here’s a great test or two if you’re not already wearing an Electronic Frontier Foundation beanie.
Panopticlick, a tool from EFF will test how easy it currently is to track you as an individual across the web. Click “test me” to launch their reader. When you get your results, there will be a link labeled “Show full results for fingerprinting” between the chart and the “Re-test your browser” button. Click for the full results and it will tell you how many people with your exact same browser/computer configuration have dropped by their site recently.
Usually if you aren’t taking any precautions your browser configuration is unique. As judged by your Chrome settings, only you could be you.
Even though I know better and occasionally do take stronger precautions, I’ve been a bit lax about my security recently and my past efforts to protect myself have crumbled: when I tested my browser settings on Panopticlick they were completely unique amongst all 230,000+ recent visitors to the site.
And even if adtrackers only had access to that small of a pool of data, because United States ISPs are not required to obscure personal information (and ISPs are even allowed to sell your site history, which is outrageous) my location has far fewer than 230k residents, so it’s safe to say that Facebook-et-al know my name and what site I’m on pretty much constantly.
To see what I mean about your ISP providing data on you, you can go to NordVPN’s homepage which will display some of your data along the top bar. Your IP address, if copy-pasted from that bar, could then be looked up on an IP Geolocation tool by a human, data collection tools will already have that reference included.
Marketing and the dark web
If you found that exercise highly unsettling, you should read up on Tor and consider subscribing to the EFF newsletter. It takes a while to learn to use Tor properly so read or watch tutorials until you could guide someone else through installing and opening Tor on your computer without looking back at the instructions. Even if you don’t intend to do anything illegal, it’s better to not form bad habits.
As a marketer, though, you might be less afraid of being followed by advertisements than most people. So let’s get back to whether or not you should be monitoring the dark web.
Most people who are chatting on the dark web simply wish to have a truly private conversation. While many are avoiding legal authorities, some are looking to avoid… us!
That means there are downsides to approaching anyone via the dark web. It would definitely be more than a faux pas to ask for someone’s email on the dark web. Even if your intent is only to send them a gift card after a negative brand experience it will be viewed as a hostile approach. If you aim that sort of outreach at the wrong person they might respond by retaliating.
One of the things for purchase on the dark web is distributed denial-of-service (DDOS) attacks. These are attempts to flood a site or service with so much traffic or activity that it has a total failure. A DDOS attack is the kind of rare but cataclysmic event your IT department mostly hopes will never occur, except in fleeting moments when they’re bored and feeling hubris.
You might remember that in 2016 a botnet called Mirai gathered thousands of internet-connected appliances to all query a DNS provider called DYN simultaneously, knocking out website hosting services to companies like Airbnb, Netflix, PayPal, Visa, Reddit, and more. It was the largest DDOS attack in history at the time and to this day no one is sure why it occurred.
Some people have suggested it was a political statement defending Julian Assanage. But another theory seems more credible: that a random, pissed-off gamer got mad at his DNS provider and decided to buy a means of punishing them.
Don’t be DYN in this equation.
If you do decide to delve into the dark web, make sure you have a talented cybersecurity team on your salaried payroll because if something happens you aren’t going to want to pay for contractor overtime.
Is there a way to monitor the dark web remotely?
You can pay someone else to watch the dark web on your behalf, although verifying their reports is a matter of trusting them if you aren’t present yourself.
Some companies that formerly marketed to IT professionals or law enforcement have now also started advertising dark web mention monitoring for brands.
Here’s a word of warning: some of the companies involved in this space are not only selling eavesdropping products. They often also operate in extremely ethically grey areas: selling police data that they’d normally need a warrant to access, assisting stalkers and paparazzi, or even indexing illegal or accidental data leaks (these often contain credit card numbers, home addresses, or social security numbers).
I’ve seen many articles recommend hiring a company called Social Links which owns the software known as Maltego, a go-to tool for cybersecurity researchers and law enforcement that has been trusted for over a decade, generally for good purposes. However, I’m choosing not to link directly to their site because I have no experience with their service and cannot personally recommend it. As always, do reputation research prior to choosing a contractor.
I hope that this explanation has helped dispel some of the rumors and confusion that circle around the dark web. Good luck building a dark web policy for your company, this guide should help kickstart your knowledge base.
Before I sign off: out of curiosity, what’s the strangest thing you’ve heard you can buy on the dark web? Or what is the direst warning you’ve received against using it? I’d love to hear either, as long as you don’t go full creepypasta in the comments!
 Kiki Schirr is a freelance marketer and writer who enjoys new technologies and cute hats from privacy advocacy groups. She has worked on multiple entrepreneurial projects, including founding a small video chat company that sunsetted before the advent of the pandemic. You can email Kiki Schirr at her full name without spaces at Gmail anytime but she does respond faster on Twitter.
Kiki Schirr is a freelance marketer and writer who enjoys new technologies and cute hats from privacy advocacy groups. She has worked on multiple entrepreneurial projects, including founding a small video chat company that sunsetted before the advent of the pandemic. You can email Kiki Schirr at her full name without spaces at Gmail anytime but she does respond faster on Twitter.
Illustration courtesy Unsplash.com




 You’re in marketing for one reason: Grow. Grow your company, reputation, customers, impact, profits. Grow yourself. This is a community that will help. It will stretch your mind, connect you to fascinating people, and provide some fun along the way. I am so glad you’re here. -Mark Schaefer
You’re in marketing for one reason: Grow. Grow your company, reputation, customers, impact, profits. Grow yourself. This is a community that will help. It will stretch your mind, connect you to fascinating people, and provide some fun along the way. I am so glad you’re here. -Mark Schaefer